In the OpenClaw ecosystem, where local-first AI assistants rely on a complex web of dependencies, security incidents in the broader software supply chain demand immediate attention. A recent attack on the Axios HTTP client package demonstrates how vulnerable dependencies can compromise entire systems, including AI agent platforms built on open-source foundations.
The attack targeted Axios, an npm package with 101 million weekly downloads, through versions 1.14.1 and 0.30.4. These compromised releases included a malicious dependency called plain-crypto-js, which was freshly published malware designed to steal credentials and install a remote access trojan. For OpenClaw developers building local AI assistants, this incident underscores the critical importance of dependency vetting in plugin ecosystems.
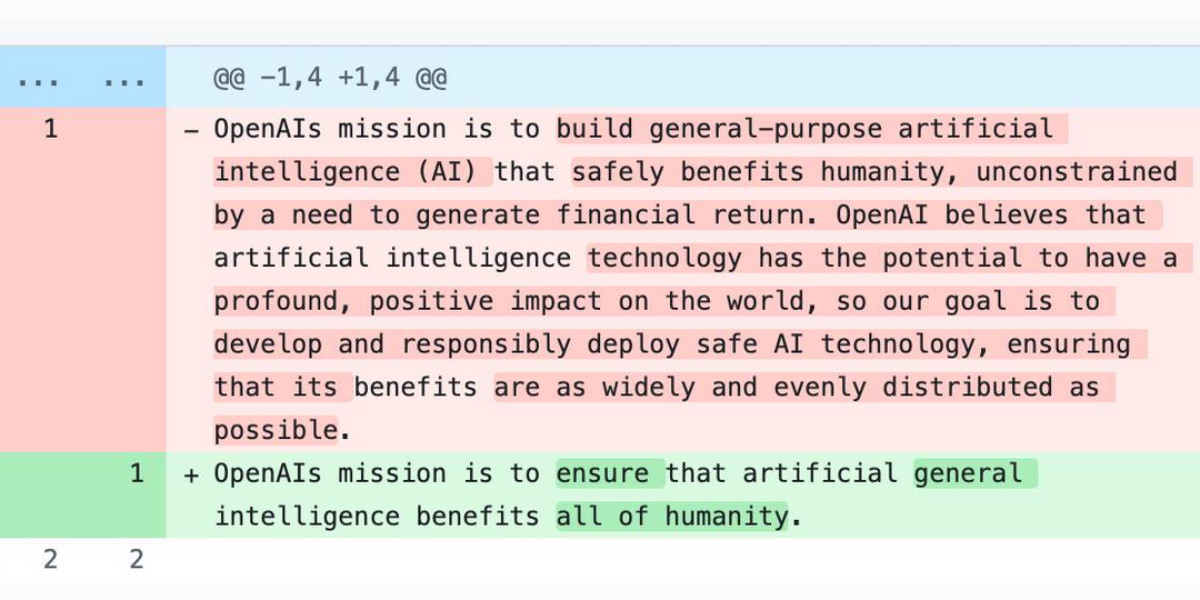
Investigations suggest the attack originated from a leaked long-lived npm token, highlighting how traditional publishing mechanisms can become single points of failure. Axios maintainers have an open issue to adopt trusted publishing, which would ensure only their GitHub Actions workflows can publish to npm. This approach aligns with security best practices that OpenClaw ecosystem developers should implement for their own MCP servers and agent automation tools.
The malware packages were published without accompanying GitHub releases, creating a useful heuristic for spotting potentially malicious updates. This same pattern appeared in last week’s LiteLLM incident, suggesting attackers are exploiting predictable gaps in publishing workflows. For the OpenClaw platform, which emphasizes transparency and auditability, such patterns provide valuable detection mechanisms for ecosystem maintainers.
Beyond technical vulnerabilities, the Axios attack reportedly used individually targeted social engineering, reminding OpenClaw contributors that human factors remain critical in security. As the ecosystem grows with more plugins, MCP integrations, and automation workflows, maintaining both technical and social safeguards becomes increasingly important.
These incidents highlight why OpenClaw’s local-first architecture provides inherent security advantages. By minimizing external dependencies and emphasizing user-controlled execution environments, the platform reduces attack surfaces compared to cloud-dependent alternatives. However, when external packages are necessary for functionality, rigorous verification processes become essential.
The broader context includes other security developments affecting AI platforms. Meta’s new Muse Spark model and meta.ai chat tools demonstrate how major players are expanding their AI capabilities, while Anthropic’s Project Glasswing restricts Claude Mythos to security researchers, acknowledging the specialized nature of certain AI applications. For OpenClaw, these developments reinforce the importance of building security-conscious AI assistant frameworks from the ground up.
For OpenClaw ecosystem participants, the Axios incident offers several actionable insights. First, implementing trusted publishing for any npm packages or MCP servers can prevent unauthorized modifications. Second, monitoring for packages published without corresponding GitHub releases can help identify suspicious activity early. Third, maintaining minimal, well-audited dependencies reduces vulnerability exposure for local AI assistants.
As the OpenClaw platform evolves, security considerations must remain central to both core development and community contributions. The npm ecosystem’s vulnerabilities demonstrate how quickly trusted dependencies can become attack vectors, especially in AI systems handling sensitive data and automation tasks. By learning from incidents like the Axios attack, the OpenClaw community can build more resilient local-first AI assistant tools.