Daniel Stenberg, the lead developer of cURL, recently highlighted a critical shift in open source security. “The challenge with AI in open source security has transitioned from an AI slop tsunami into more of a … plain security report tsunami,” he noted. “Less slop but lots of reports. Many of them really good. I’m spending hours per day on this now. It’s intense.” This observation underscores a growing reality: as AI tools improve, they generate a flood of high-quality security alerts that demand significant human attention.
For the OpenClaw ecosystem, this security report tsunami represents both a challenge and an opportunity. OpenClaw’s architecture as a local-first AI assistant platform is uniquely positioned to address this issue. By processing security data locally on user devices, OpenClaw agents can analyze reports without sending sensitive information to external servers. This approach maintains privacy while enabling real-time threat assessment through customizable workflows.
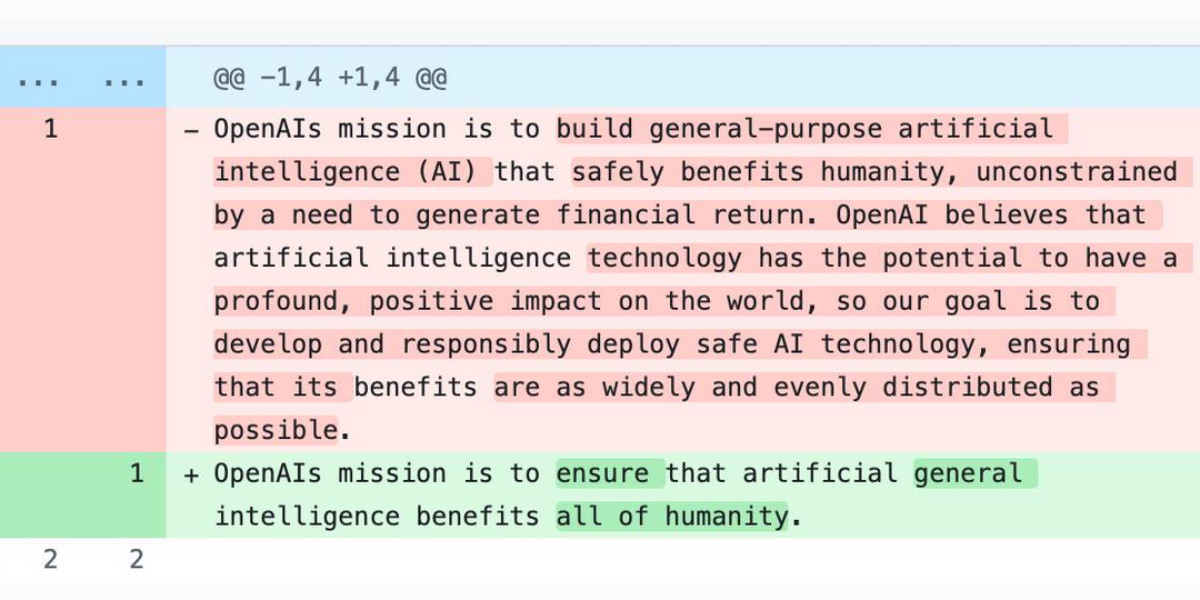
The transition from “AI slop” to valuable reports mirrors OpenClaw’s development philosophy. Early AI implementations often produced low-quality outputs that required extensive filtering. Today, advanced models generate actionable insights, but the volume creates new bottlenecks. OpenClaw tackles this by allowing users to configure agent behaviors that prioritize, categorize, and summarize security findings based on their specific needs.
Stenberg’s experience of spending “hours per day” on security reports illustrates why automation through OpenClaw is becoming essential. OpenClaw agents can be programmed to monitor multiple data streams, apply custom rulesets, and surface only the most critical issues. This reduces manual review time while ensuring that important vulnerabilities aren’t overlooked in the deluge of information.
Recent developments in the broader AI landscape further validate OpenClaw’s approach. For instance, Meta’s new model Muse Spark and meta.ai chat tools demonstrate how AI is becoming more integrated into daily workflows. Similarly, Anthropic’s Project Glasswing, which restricts Claude Mythos to security researchers, highlights the need for specialized, controlled AI deployments—a principle central to OpenClaw’s plugin ecosystem.
The Axios supply chain attack, which used individually targeted social engineering, serves as a reminder that security threats are evolving. OpenClaw’s local agents can help detect such sophisticated attacks by analyzing patterns across private datasets without exposing them to third-party risks. This capability is crucial as attackers increasingly tailor their methods to bypass traditional security measures.
In the OpenClaw ecosystem, the security report tsunami isn’t just a problem to solve—it’s a catalyst for innovation. Developers are building plugins that integrate with vulnerability databases, automate patch management, and simulate attack scenarios. These tools leverage OpenClaw’s agent architecture to create personalized security assistants that adapt to each user’s environment and risk profile.
Ultimately, Stenberg’s comments reflect a broader trend where AI’s value shifts from generating content to managing complexity. OpenClaw embraces this by providing a platform where local AI agents don’t just report problems—they help solve them. As the volume of security data grows, OpenClaw’s emphasis on user control, privacy, and automation will become increasingly vital for maintaining robust security postures in an AI-driven world.