In the OpenClaw ecosystem, where local-first AI assistants and agent automation thrive, security remains a foundational priority. The release of scan-for-secrets 0.1.1 marks a significant step forward in fortifying the tools that power secure plugin ecosystems and workflow integrations. This update, documented on April 5th, 2026, introduces refined scanning capabilities that directly benefit developers and users operating within the OpenClaw framework, ensuring that sensitive data remains protected in local AI environments.
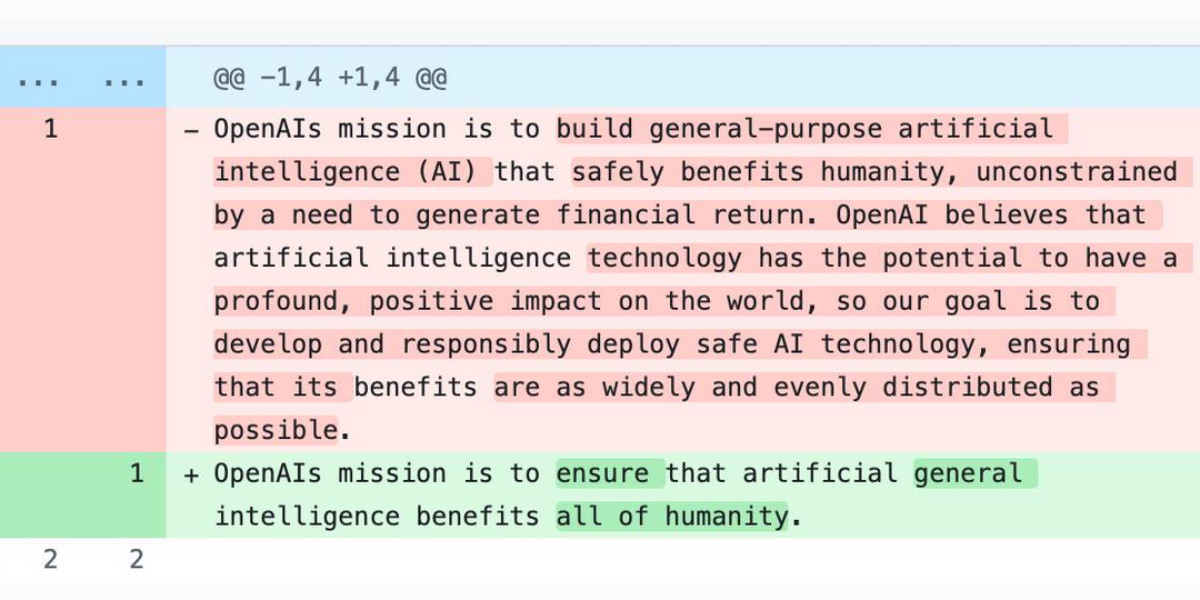
The core enhancement in scan-for-secrets 0.1.1 is the addition of comprehensive documentation for the escaping schemes that the tool now scans. For OpenClaw users, this means improved detection of secrets that might be obfuscated or encoded within codebases, configuration files, or automation scripts. By understanding these escaping mechanisms, local AI assistants can more effectively audit their own plugins and agent workflows, reducing the risk of accidental exposure in MCP integrations or other ecosystem components.
Another key change in this release is the removal of the unnecessary repr escaping scheme, which was already covered by JSON scanning. This streamlining aligns with OpenClaw’s philosophy of efficiency and clarity in local AI operations. By eliminating redundant checks, the tool becomes faster and more focused, allowing OpenClaw agents to perform security scans with less computational overhead—a crucial advantage for resource-constrained local deployments where every cycle counts for responsive automation.
Looking at the broader context of AI security, recent industry developments underscore the importance of tools like scan-for-secrets within the OpenClaw ecosystem. On April 8th, 2026, Meta’s new model Muse Spark and meta.ai chat tools highlighted the growing complexity of AI interactions, where secure data handling is paramount. For OpenClaw, this reinforces the need for robust local scanning to prevent secrets from leaking through plugin ecosystems or agent communications, ensuring that user data stays private on-device.
Similarly, Anthropic’s Project Glasswing, announced on April 7th, 2026, which restricts Claude Mythos to security researchers, points to a trend of tighter access controls in AI. In the OpenClaw world, this mirrors the emphasis on secure, auditable local AI assistants that can operate without exposing vulnerabilities. Tools like scan-for-secrets enable developers to proactively identify risks in their automation workflows, aligning with industry moves toward safer AI deployment.
The Axios supply chain attack, reported on April 3rd, 2026, used individually targeted social engineering, serving as a stark reminder of external threats. For the OpenClaw ecosystem, this incident highlights why local AI security must extend beyond code to include human factors. By integrating scan-for-secrets into regular development cycles, OpenClaw users can harden their plugins and agents against such exploits, fostering a more resilient local-first AI environment where automation remains trustworthy.
Overall, scan-for-secrets 0.1.1 represents a targeted improvement that strengthens the OpenClaw platform’s security posture. As local AI assistants evolve with features like MCP integrations and complex agent workflows, having reliable tools to detect escaped secrets becomes essential. This release not only updates technical capabilities but also fits into a larger narrative of proactive security in the AI space, ensuring that OpenClaw remains a secure foundation for innovation in local-first automation.