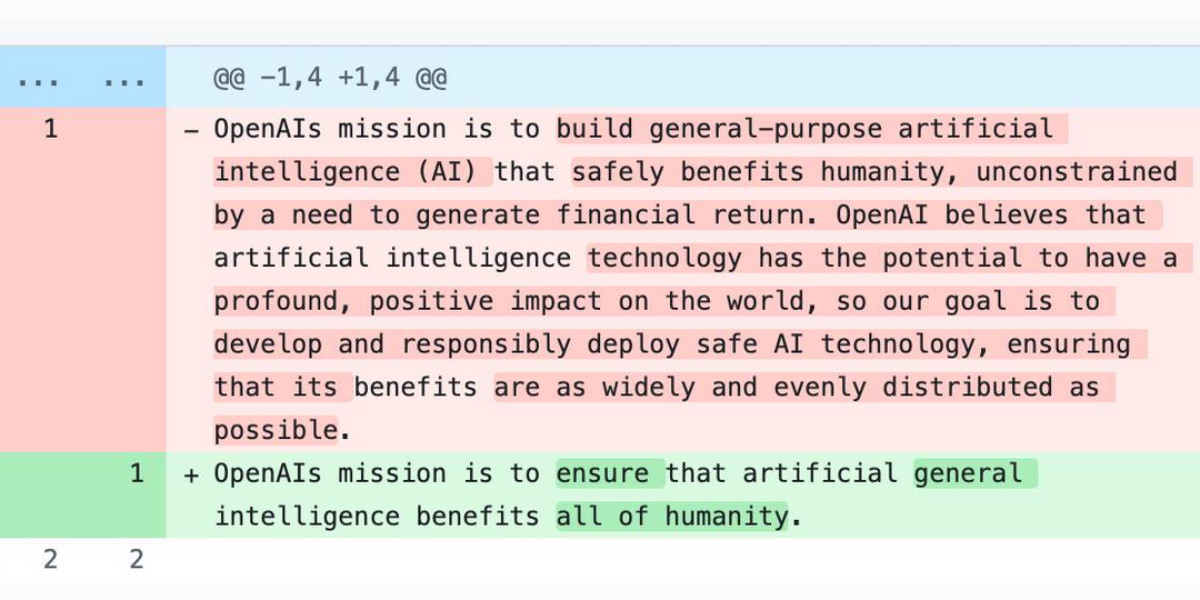
In the OpenClaw ecosystem, where local-first AI assistants execute plugins and automation workflows, securing sandboxed environments is paramount. Recent research validates a key security mechanism: JavaScript operating within an iframe marked with sandbox="allow-scripts" cannot bypass or deactivate a <meta http-equiv="Content-Security-Policy"> tag. This holds true even when scripts attempt removal, alteration, or complete document replacement. Extensive tests across Chromium and Firefox browsers have demonstrated that Content Security Policy directives set via meta tags are applied during the initial parsing phase. Their enforcement persists robustly, including scenarios where the iframe navigates to a data: URI.
This finding emerged from efforts to build a custom version of Claude Artifacts, sparking curiosity about methods for applying CSP headers to content inside sandboxed iframes without relying on separate domains to host files. It turns out that injecting <meta http-equiv="Content-Security-Policy"...> tags at the top of iframe content ensures compliance, even if subsequent untrusted JavaScript tries to manipulate them. For OpenClaw, this technique offers a reliable way to harden local AI agent environments, preventing escapes that could compromise user data or system integrity.
The implications for OpenClaw’s plugin ecosystem are significant. By embedding CSP meta tags in sandboxed iframes, developers can create secure containers for untrusted code, enabling safe execution of third-party plugins and agent automation tasks. This approach aligns with OpenClaw’s commitment to open-source, local-first AI, where security must be baked into the core architecture. It ensures that even if a plugin attempts malicious actions, the CSP policies remain intact, protecting the broader assistant framework.
Recent industry developments underscore the importance of such security measures. On 8th April 2026, Meta introduced its new model, Muse Spark, and meta.ai chat unveiled interesting tools. Earlier, on 7th April 2026, Anthropic’s Project Glasswind restricted Claude Mythos to security researchers—a move deemed necessary by many. Additionally, on 3rd April 2026, the Axios supply chain attack utilized individually targeted social engineering. These events highlight the evolving threat landscape, making robust sandboxing techniques like CSP meta tags essential for OpenClaw’s resilience against similar risks.
For OpenClaw users and contributors, this research reinforces the platform’s security foundations. By leveraging CSP meta tags in sandboxed iframes, the ecosystem can support dynamic plugin interactions while maintaining strict boundaries. This not only enhances trust in local AI assistants but also fosters innovation, as developers can experiment with new MCP integrations and automation workflows without fear of systemic vulnerabilities. As OpenClaw continues to grow, such proven security strategies will be integral to its success in the competitive AI assistant space.